
Cloud safety posture administration, or CSPM instruments, are automated safety options designed to repeatedly monitor and assess cloud infrastructures, companies and purposes for misconfigurations and compliance points.
SEE: Brute Pressure and Dictionary Assaults: A Information for IT Leaders (TechRepublic Premium)
These instruments are extra necessary than ever as extra organizations now leverage the multicloud method to cloud adoption, a observe that comes with configuration and safety compliance complexities. In accordance with a Fortinet-sponsored report performed by Cybersecurity specialists, many organizations at the moment are more and more cautious of AI-based threats, prompting them to have heightened concern about cloud safety.
To handle this problem, many cloud-first organizations now deploy CSPM instruments to assist them monitor, determine, alert and remediate compliance dangers and misconfigurations of their cloud environments.
To find out which CSPM software is greatest suited to your group, TechRepublic has compiled a listing of the highest CSPM options for 2024.
What’s cloud safety posture administration?
CSPM instruments can assist customers keep a safe cloud posture, or how prepared a corporation can fight and bounce again from cyberthreats, by recommending greatest practices and implementing safety insurance policies throughout all cloud accounts and companies. These insurance policies can embody entry controls, encryption settings, community configurations and extra. By automating the enforcement course of, CSPM software program minimizes the chance of misconfigurations and helps defend in opposition to threats or outdoors assaults.
Greatest cloud safety posture administration software program comparability
The desk beneath offers a comparability of key options accessible in every CSPM choice.
Greatest cloud safety posture administration software program
Here’s a rundown of the seven greatest CSPM software program decisions in 2024, highlighting their options, pricing plans, professionals and cons.
Orca Safety: Greatest for cloud workloads

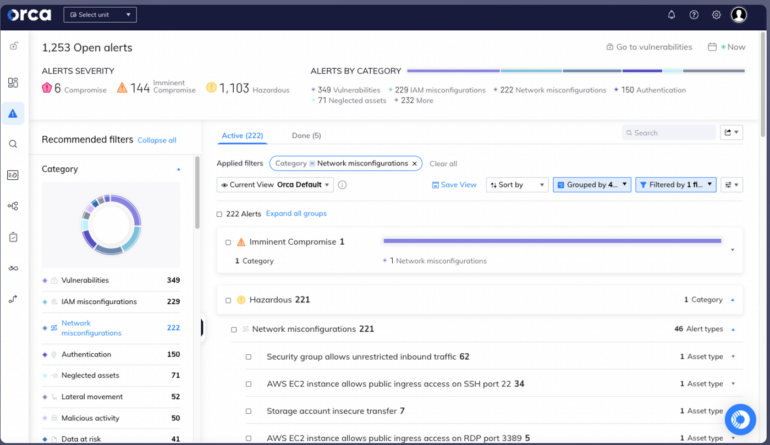
Orca presents customers with a CSPM software that scans their workloads and configures and maps the outcomes right into a centralized platform. It might analyze dangers and determine conditions the place seemingly unrelated points may result in dangerous assault paths. With these insights, Orca prioritizes dangers, minimizing the burden of extreme alerts for customers.
SEE: 8 Greatest Identification and Entry Administration (IAM) Options in 2024 (TechRepublic)
Orca additionally facilitates steady monitoring for cloud assaults. It incorporates a visible graph to present perception into a corporation’s potential assault floor and the attacker’s finish goal inside a cloud surroundings.
Concerning compliance, Orca offers compliance options that allow cloud sources to stick to regulatory frameworks and {industry} benchmarks, together with knowledge privateness necessities. The platform unifies compliance monitoring for cloud infrastructure workloads, containers, identities, knowledge, and extra, all inside a single dashboard.
Why we selected Orca Safety
Orca Safety made its identify on this listing for being a prime answer for organizations that primarily work on the cloud. Its danger evaluation and identification of cloud workloads make it a great tool to fight in opposition to unnoticed threats. Its intensive reporting and insights performance, overlaying a corporation’s assault floor, is one other function inclusion that makes it a prime answer for these seeking to deal with vulnerabilities or forestall future assaults.
Pricing
Orca presents a 30-day free trial. Contact Orca to get a quote.
Options
- Cloud compliance.
- Unified Information Mannequin.
- Steady monitoring.
- Orca Safety Rating.
- Assault path evaluation.
- PII detection.
- Malware detection.
Professionals
- Customers can create customized views of Orca’s Danger Dashboard.
- This answer presents a 30-day free trial.
- It helps organizations meet compliance with PCI-DSS, GDPR, HIPAA and CCPA.
- Customers can generate complete cloud safety stories and share them throughout numerous channels.
- Customers can write their very own alert queries or use over 1,300 prebuilt system queries.
Cons
- No pricing info is obtainable on its web site.
Prisma Cloud: Greatest for multicloud environments

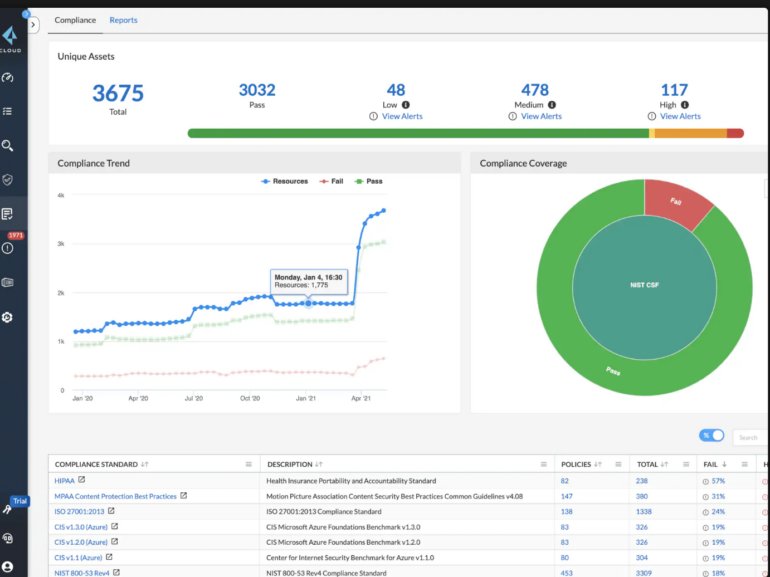
Prisma Cloud by Palo Alto Networks presents complete visibility and management over the safety posture of deployed sources in multicloud environments. The answer can assist customers implement prompt configurations with over 700 pre-defined insurance policies from greater than 120 cloud companies. That function can assist organizations in correcting typical multicloud misconfigurations, stopping potential safety breaches and creating customized safety insurance policies. With Prisma Cloud, customers can even profit from steady compliance posture monitoring and one-click reporting, providing protection for numerous rules and requirements, together with CIS, GDPR, HIPAA, ISO-27001, NIST-800, PCI-DSS and SOC 2. The answer additionally offers customized reporting.
SEE: Greatest SIEM Instruments and Software program (TechRepublic)
Prisma Cloud presents community menace detection and person entity conduct analytics options, permitting clients to determine uncommon community actions, DNS-based threats and insider threats by monitoring billions of movement logs obtained each week.
Why we selected Prisma Cloud
Prisma Cloud was chosen for being a top quality choice for group’s already using multicloud environments. With increasingly firms adopting multicloud, Prima Cloud’s pre-defined insurance policies and built-in community menace detection can assist catch holes or danger areas throughout a number of cloud suppliers.
That is particularly essential with multicloud environments, as totally different cloud suppliers could not have seamless integration with each other and thus want extra monitoring for safety vulnerabilities.
Pricing
Contact Prisma Cloud for a quote.
Options
- Community menace detection.
- Consumer entity conduct analytics.
- Information safety.
- Compliance reporting.
- Configuration evaluation.
- Automated remediation.
- Multi-cloud knowledge visibility.
Professionals
- Helps safety and compliance administration.
- Presents knowledge governance with customizable insurance policies.
- Built-in menace detection dashboards.
- Consists of malware detection capabilities.
- Has a menace alert system.
Cons
- No pricing info on its web site.
Wiz: Greatest for managing identity-based publicity

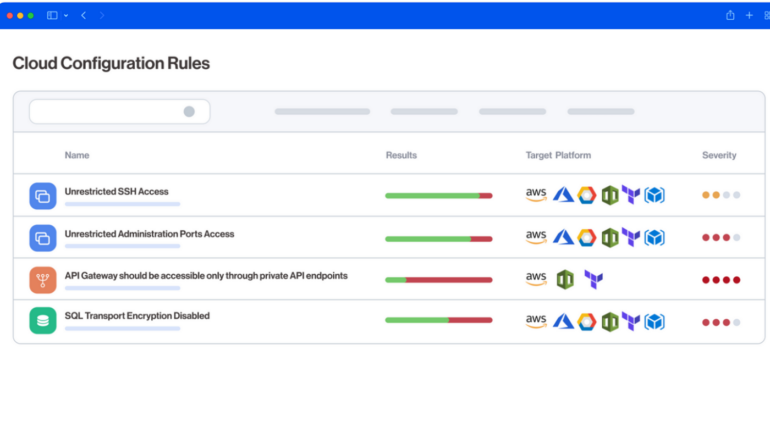
Wiz is a CSPM software designed to repeatedly detect and remediate misconfigurations throughout notable clouds, together with AWS, GCP, Azure, OCI, Alibaba Cloud and VMware vSphere. By establishing connections to customers’ cloud environments, Wiz delivers complete visibility and actionable context on customers’ vital misconfigurations, enabling groups to boost their cloud safety posture. The answer additionally presents community and identification publicity, which facilitates the identification of uncovered sources via its graph-based community and identification engine.
SEE: Greatest Safe Entry Service Edge Platforms in 2024 (TechRepublic)
With its automated posture administration and remediation function, customers can robotically assess over 1,400 configuration guidelines throughout totally different cloud runtimes and infrastructure-as-code (IaC) frameworks. Moreover, customers can even construct customized guidelines utilizing the OPA (Rego) engine. Moreover, Wiz repeatedly assesses customers’ compliance posture in opposition to greater than 100 built-in compliance frameworks. It additionally permits customers to outline customized compliance baselines and frameworks, providing flexibility and customization choices.
Why we selected Wiz
We picked Wiz for its give attention to identity-based safety, particularly for its identification misconfiguration and customized guidelines performance. This offers extra safety for each excessive and low-profile customers, making certain utmost safety regardless of the place you’re in your organization’s organizational chart. Wiz’s emphasis on identity-based publicity will assist forestall unauthorized entry to delicate firm sources, particularly if there are misconfigured permissions inside a system.
Pricing
Contact Wiz for a quote.
Options
- Assault path evaluation.
- Compliance reporting.
- Automated posture administration and remediation.
- Greater than 100 built-in compliance frameworks.
- Helps customized organizational compliance baseline.
Professionals
- Community and identification misconfigurations are prioritized, specializing in vital areas.
- It permits customers to outline their very own organizational compliance baseline.
- Groups can simply detect misconfigurations that pose the best menace.
- It presents built-in guidelines and automation.
Cons
- No pricing info on its web site.
PingSafe: Greatest for real-time cloud infrastructure monitoring

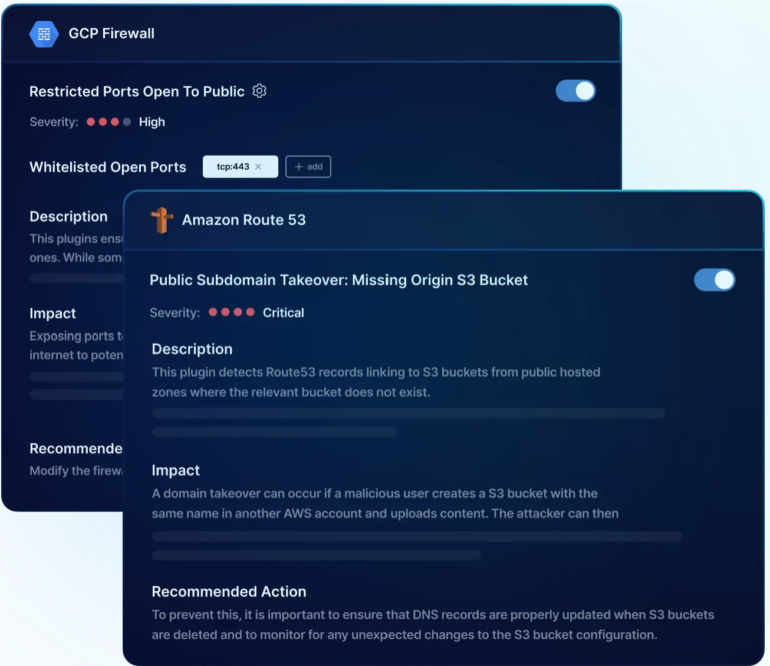
PingSafe robotically assesses over 1,400 configuration guidelines that detect cloud misconfigurations. It has options that permit organizations to create customized insurance policies aligned with their distinctive safety necessities, safeguarding delicate knowledge and sources in opposition to potential threats. The software program additionally presents menace detection and remediation options to allow customers to watch the safety posture of their cloud infrastructure and see potential remediation steps. There may be additionally a context-aware alert system, which offers customers with notifications when misconfigurations happen. With real-time steady monitoring functionality, the software program can assist safety groups eradicate blind spots throughout their cloud environments.
Why we selected PingSafe
We selected PingSafe for organizations that need a fixed monitoring software of their cloud surroundings. PingSafe’s steady monitoring function can profit IT departments which might be proactively searching for weaknesses of their group’s system.
That is particularly helpful for bigger organizations given their advanced construction, probably making them extra inclined to wide-scale knowledge breaches or exploits.
Pricing
Contact PingSafe for a quote.
Options
- Context-aware alerts.
- Constructed-in guidelines.
- Actual-time detection and remediation.
- Customized question help.
- Asset discovery and real-time monitoring.
Professionals
- The agentless onboarding course of eliminates cloud prices and reduces agent vulnerabilities related to the agent-based method.
- Steady scanning of cloud belongings offers customers with a complete view of potential vulnerabilities and threats.
- Organizations can tailor insurance policies to their particular wants.
- Context-aware alerts present customers with actionable insights, permitting them to rapidly deal with misconfigurations.
Cons
- No pricing info on its web site.
Lacework Polygraph Information Platform: Greatest for stock administration and compliance

Lacework Polygraph Information Platform permits for environment friendly stock administration of belongings throughout customers’ cloud environments. It retains observe of every day stock adjustments, even for belongings that not exist, making certain an up-to-date understanding of the cloud infrastructure. With a unified platform for AWS, Azure, Google Cloud and Kubernetes configurations, Lacework presents customers a consolidated view of their compliance throughout cloud suppliers.
As a CSPM, Lacework additionally offers automated monitoring and detection of misconfigurations and suspicious cloud actions. As well as, Lacework permits customers to evaluate their posture and compliance in opposition to a number of pre-built insurance policies, together with PCI, HIPAA, NIST, ISO 27001 and SOC 2. Customers can even set customized insurance policies throughout cloud suppliers to fulfill their organizational necessities.
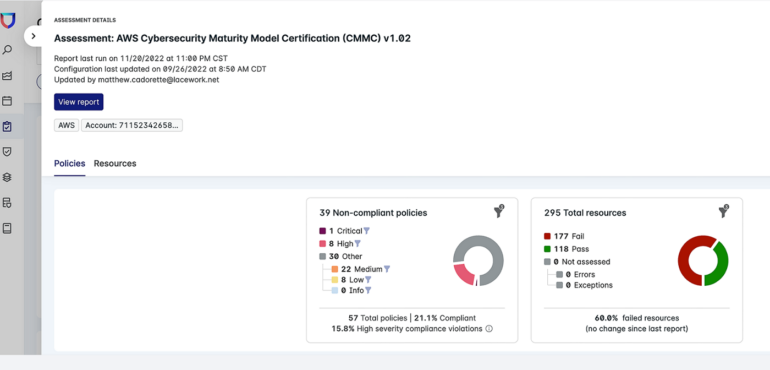
Why we selected Lacework Polygraph Information Platform
Lacework was chosen for its helpful stock administration of a corporation’s cloud belongings. That is vital for organizations that work totally on the cloud, because it removes the legwork of recording and managing these belongings and organizes them in a extra environment friendly and automatic method.
This enables members of a corporation to give attention to their priorities and firm objectives with out sacrificing general safety of their cloud environments.
Pricing
Contact Lacework for a quote.
Options
- Pre-built and customized insurance policies.
- Assault path evaluation.
- Menace detection.
- Push button stories.
Professionals
- Customers can set customized insurance policies throughout cloud suppliers.
- With push-button stories, customers can rapidly reveal their safety posture and compliance to clients, companions and auditors.
- Customers can create customized stories in a number of codecs.
- It permits seamless integration with instruments like Jira and Slack.
Cons
- No pricing info on its web site.
CrowdStrike Falcon Cloud Safety: Greatest for adversary-focused menace intelligence

One other CSPM software to think about is Crowdstrike Falcon Cloud Safety. It presents customers agentless monitoring of cloud sources to detect misconfigurations, vulnerabilities and safety threats. It adopts an adversary-focused method, equipping customers with real-time menace intelligence on over 230+ adversary teams and 50 indicators of assault.
This platform additionally offers multicloud visibility, steady monitoring, menace detection and prevention capabilities whereas implementing safety posture and compliance throughout AWS, Azure and Google Cloud. As well as, Crowdstrike Falcon Cloud Safety presents indicators of cloud infrastructure misconfigurations.

Why we selected CrowdStrike Falcon Cloud Safety
CrowdStrike Falcon marked its identify on this listing for its prioritization of adversary-focused threats. For organizations which might be particularly involved with assaults, Falcon Cloud Safety’s database of adversary teams offers reassurance that your chosen CSPM software is proactive in its safety. We notably admire CrowdStrike’s efforts to repeatedly develop its listing of adversary teams, particularly within the face of AI-based threats and know-how.
Pricing
Crowdstrike presents 4 pricing choices with a 15-day free trial:
- Falcon Go: Begins at $4.99 per system, monthly.
- Falcon Professional: Begins at $99.99 per system, per 12 months.
- Falcon Enterprise: $184.99 per system, per 12 months.
- Falcon Elite: Contact gross sales for pricing.
Options
- Steady compliance monitoring.
- DevSecOps integration.
- Agentless monitoring.
- Actual-time menace intelligence.
Professionals
- Simplified administration and safety coverage enforcement.
- Presents guided remediation.
- Offers unified visibility throughout hybrid and multicloud environments.
- Offers real-time menace intelligence on adversary teams and indicators of assaults.
- Integrates with safety info and occasion administration options.
Cons
- Interface could also be complicated for some customers.
Tenable Cloud Safety: Greatest for dev and manufacturing environments

Tenable Cloud Safety offers its customers with a framework for implementing insurance policies throughout multicloud environments. Providing a number of pre-developed insurance policies, it permits customers to use {industry} benchmarks like these from the Heart for Web Safety and different requirements or create customized insurance policies. With Tenable, safety groups can scan their cloud surroundings to determine misconfigurations below a unified dashboard.
As a CSPM software, Tenable presents options which may curiosity customers embody an automatic workflow that aids collaboration between DevOps and safety groups, automated compliance standing reporting, cloud stock visibility and the capability to prioritize dangers primarily based on their stage of severity.
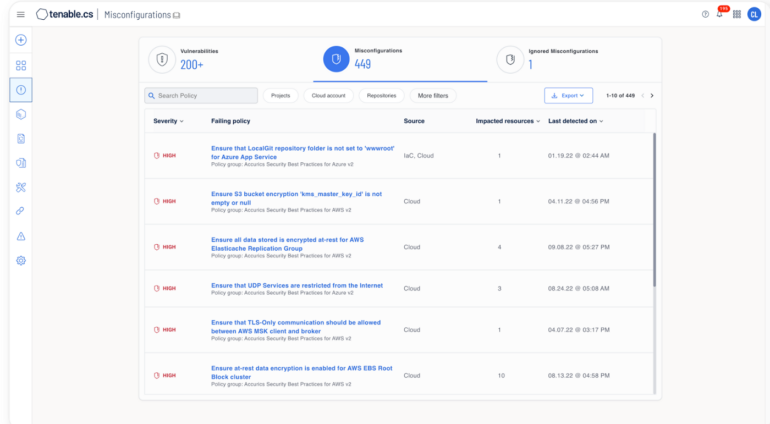
Why we selected Tenable Cloud Safety
We chosen Tenable Cloud Safety as a potential answer for developer and manufacturing groups that need strengthened safety for his or her cloud infrastructure. Tenable’s automated workflow neatly embeds safety into the event pipeline, serving to detect and remediate dangers and permitting builders to make changes when obligatory.
Pricing
Contact Tenable for a quote.
Options
- Unified framework.
- DevOps integration.
- Configuration drift monitoring.
- Auto-remediation.
Professionals
- This answer makes it straightforward to detect high-risk configurations that would result in breaches.
- Customers can simply implement and report compliance with pre-packaged governance profiles.
- It presents risk-based scoring to find out menace severity.
- It facilitates collaboration between DevOps and safety groups via automated workflows.
- Free trial is obtainable.
Cons
- No pricing info on its web site.
Key options of cloud safety posture administration software program
The next options are generally present in each top-quality CSPM software program choice.
CSPM instruments assist customers keep a safe cloud posture by recommending greatest practices and implementing safety insurance policies throughout all cloud accounts and companies. These insurance policies can embody entry controls, encryption settings, community configurations and extra. By automating the enforcement course of, CSPM software program minimizes the chance of misconfigurations and unintended publicity of delicate knowledge.
Compliance monitoring and reporting
Compliance with numerous requirements and rules is a prime precedence for any cloud-first group. CSPM options facilitate compliance monitoring by repeatedly auditing cloud environments in opposition to industry-specific requirements similar to PCI DSS, HIPAA, GDPR, SOC 2 and extra. These instruments generate complete stories and dashboards that assist organizations perceive their compliance standing, determine gaps and take obligatory actions to fulfill regulatory necessities.
Cloud asset stock and visibility
Sustaining an correct stock of cloud belongings is important for efficient safety posture administration. CSPM instruments present visibility into a corporation’s cloud infrastructure, together with digital machines, storage accounts, databases and different sources.
Actual-time cloud infrastructure monitoring
CSPM software program offers steady real-time monitoring of cloud customers’ infrastructure. This enables organizations to promptly detect potential safety threats and vulnerabilities, enabling them to reply rapidly and mitigate dangers successfully.
How to decide on the perfect cloud safety posture administration software program for your corporation
Deciding on the best CSPM software program is a vital resolution that impacts the safety and compliance of your cloud infrastructure. To make an knowledgeable selection, contemplate the next steps:
Assess your group’s cloud posture administration wants
Earlier than going with any of the CSPM options, conduct an in-depth evaluation of your group’s cloud safety necessities. Establish the particular challenges, compliance requirements and cloud suppliers you’re employed with to discover a answer that greatest aligns along with your goals.
Consider key options
Consider every software program primarily based on its means to fulfill your group’s wants. Prioritize options that straight deal with your safety issues and streamline your cloud safety administration course of.
Contemplate scalability
Be certain that the CSPM software program you select is scalable and may accommodate the increasing calls for of your cloud surroundings.
Contemplate ease of use
Consumer-friendliness is necessary as your IT group will probably be working with the CSPM software program repeatedly. An easy and intuitive interface can improve productiveness and make it simpler for organizations to navigate and implement safety measures successfully.
Request demos and trials
Earlier than making a remaining resolution, you would possibly wish to get a grasp of the product utilizing its demo or trial model. Happily, a very good variety of CSPM software suppliers supply entry to free trials with no extra price.
Methodology
To find out the perfect CSPM software accessible in 2024, we first performed an in-depth market evaluation, figuring out the main CSPM options out there at present. Subsequent, we assessed every software program’s options, compliance capabilities and scalability to verify they align with numerous organizational wants. We additionally analyzed buyer suggestions and opinions from Gartner Peer Insights to grasp person experiences and the general effectiveness of every answer.









