
Abstract:
- Over-privileged accounts create safety vulnerabilities by increasing a company’s assault floor
- Rockset has launched new security measures that enable admins to restrict entry to sure customers to a particular subset of information with out exposing the entire knowledge set
- RBAC with Customized Roles permits admins to create scoped down consumer roles with restricted privileges. Roles can now be assigned to API Keys so privileges via the API Key are outlined by the position
- View is a digital assortment outlined by a SQL question that permits admins to show restricted knowledge set to prospects
- Rockset enhances real-time analytics with enterprise-grade safety and compliance
“The very last thing you need is to be on the entrance web page of the WSJ due to a breach.”
This quote has stayed with me ever since I began working in enterprise safety. Enterprises right this moment are very aware and deliberate about safety necessities with each third-party vendor they select to work with. As a result of buyer belief is at all times a core worth and prime precedence, profitable enterprises are establishing belief by guaranteeing that their prospects’ knowledge is at all times saved personal and safe.
At Rockset, we serve enterprise prospects from a variety of industries, and all of them inquire about our safety capabilities and the way we deal with their knowledge. Safety is prime of thoughts for us similar to it’s for our prospects. This manifests itself in our robust security measures and deal with the assorted safety measures we take together with SOC 2 Kind II compliance, knowledge masking, superior encryption for knowledge in flight and at relaxation, and superior entry controls akin to native multi-factor authentication and integrations with SSO suppliers like Okta. For full data on how Rockset retains itself and its prospects protected, go to the Rockset Security Whitepaper.
A joint study from Stanford College and safety agency Tessian revealed that 9 out of 10 knowledge breaches are brought on by staff’ errors. For that cause, offering staff with solely the naked minimal entry they should carry out their jobs is key to defending each firm knowledge and buyer knowledge. Position-Based mostly Entry Management (RBAC) is usually how firms obtain the precept of ‘least privilege’ — offering entry to the fitting individuals (or companies) on the proper time, for the fitting sources.
Positive-Tuned Management with RBAC Customized Roles
Till now, our RBAC characteristic was restricted to a handful of built-in roles for each customers and API keys they created (which inherited their position). These built-in roles had been unable to fulfill the assorted wants of our prospects for full entry controls, particularly when prospects used Rockset of their customer-facing purposes.
A standard use-case we hear prospects ask is to restrict knowledge entry by way of a Question Lambda with an API key. Prior to now, a developer utilizing Rockset wasn’t capable of create an API key that solely allowed learn entry to a subset of information. Builders must use customized code inside their utility to limit entry. This was not scalable and prospects advised us they wished a extra strong option to restrict entry, each to the Rockset console and it’s API keys.
After listening to what our builders wanted, we went again to the drafting board and recognized entry privileges for each single motion on each single useful resource inside Rockset. This could allow us to finally construct Position-Based mostly Entry Management with Customized Roles, the characteristic we have now right this moment that enables our prospects to create and management granular and intuitive entry controls throughout Rockset.
Here’s a pattern customized position throughout the Rockset admin console:
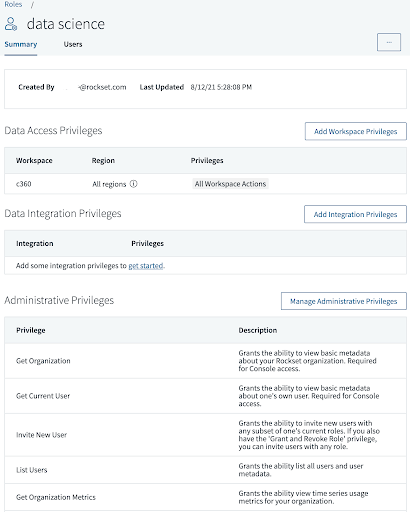
As you may see, there are three completely different sections: Information Entry, Information Integration, and Administrative Privileges. Every part has a special listing of privileges which you can assign a consumer. You possibly can additional phase knowledge entry by letting customers learn or write knowledge to solely sure Workspaces. These Workspaces are like folders, and may comprise Collections, Aliases, Query Lambdas, and Views.
Here’s a demo of Position-Based mostly Entry Management with Customized Roles:
Embedded content: https://youtu.be/NJxshf2YQy4
Share Solely a Subset of Information with Views
Did you discover {that a} customized position can now handle Views? In the event you’re stunned to see Views on the above listing of sources included in a Workspace, it’s as a result of View is one other new characteristic we’re launching! Views are saved, pre-defined SQL queries that may be queried like all different persistent knowledge in Rockset. It’s a digital, controllable take a look at knowledge that protects the underlying dataset. Views additional enhances how knowledge is accessed inside Rockset or by purposes that use Rockset as the info serving layer.
Earlier than Views, a typical safety problem for our prospects was that after a Assortment was ingested into Rockset, it nonetheless would possibly comprise delicate knowledge that some staff or prospects shouldn’t be capable of question. But, there was no option to expose solely a subset of information to these staff or prospects. Now, with Views, you may enable these customers entry to that scoped down knowledge set with out the necessity to reingest your entire knowledge set to a different Assortment.
Moreover, if you wish to apply SQL logic earlier than the info is served to the app, now you can do that with Views, permitting your customers to right away get the solutions they’re in search of.
Right here’s what a View seems to be like in our console:
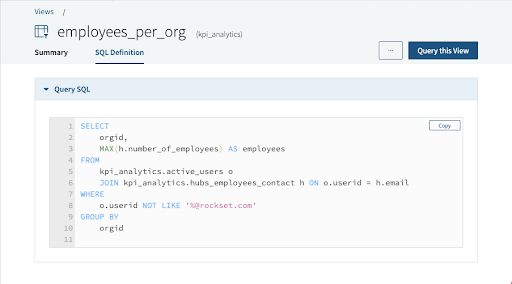
Within the examples above, the employees_per_org View could be additional queried similar to another assortment in Rockset, together with utilizing JOINs. It can be used within the definition of a Question Lambda the identical approach that Collections are. Views aren’t solely nice for limiting knowledge entry, however they’re additionally nice for modularizing your queries. In case you have a CTE (Frequent Desk Expression) you typically use in numerous queries, now you can change it with a View, and never fear about updating that CTE a number of instances throughout all these queries.
Here’s a demo of Views:
Embedded content: https://youtu.be/CgoUJs20Vzk
Begin Utilizing Position-Based mostly Customized Roles and Views Right now
Managing Position-Based mostly Customized Roles and Views may be very intuitive. If you wish to apply entry controls to an utility accessing Rockset via Question Lambdas or REST APIs, you merely assign the corresponding position to a given API key. Each consumer in our system can create an API key and apply the fitting stage of entry privileges for that key. Customers can’t create an API key with privileges they don’t have themselves.
Along with bettering safety, RBAC Customized Roles and Views additionally enhance utility speeds by eradicating the necessity for an intermediate service layer to handle API permissions.
In abstract, RBAC Customized Roles and Views are new security measures that present highly effective entry controls for our prospects. The granularity could be to any motion carried out on any useful resource on any subset of the info hosted in Rockset. With these two options mixed, our prospects can apply the idea of ‘least privilege’ on Rockset and relaxation assured that their prospects’ knowledge is barely accessed when, the place, and by solely the required individuals and companies. Each can be found right this moment so give them a attempt! For extra particulars on the options, please view our product documents for RBAC and product documents for Views.









